Linux Router with VPN on a Raspberry Pi
Rationale
This guide demonstrates how to set up a Linux router with a VPN tunnel. You will need a second ethernet adapter. If you are using a Raspberry Pi, then you can use something like this Apple USB Ethernet Adapter as it contains a ASIX AX88772 which has good Linux support.
You may choose to also buy a Real Time clock. If you don't have an RTC, the time is lost when your Pi is shut down. When it is rebooted, the time will be set back to Thursday, 1 January 1970. As this is earlier than the creation time of your VPN certificates OpenVPN will refuse to start, which may mean you cannot do DNS lookups over VPN.
For wireless, a separate access point was purchased (Ubiquiti UniFi AP) because it contains a Atheros AR9287 which is supported by ath9k.
I chose a Raspberry Pi because it's inexpensive. I was not concerned with getting high PPS (Packets Per Second). You could choose to use an old x86/amd64 system instead. If I had better internet I'd probably go with an offering from Soekris such as the net6501 as it would have a much lower power consumption than a generic x86_64 desktop processor.
If you want to route speeds above 100 Mbit/s you'll want to make use of hardware encryption like AES-NI. The Soekris offerings have the option of an additional hardware encryption module (vpn1411). Another option is to use a Mini ITX motherboard, with a managed switch. I chose the Ubiquiti ES-16-150W.
If you wish to use IPv6 you should consider looking at Linux Router with VPN on a Raspberry Pi (IPv6) as the implementation does differ slightly from this tutorial.
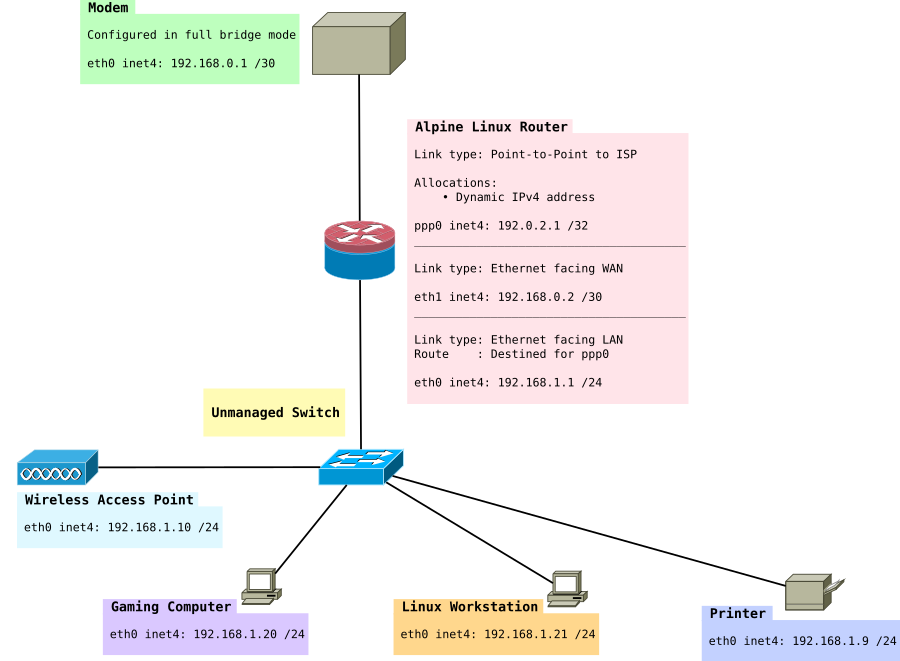
The network in this tutorial looks like this:
Installation
This guide assumes you're using Alpine Linux from a micro SD card in ramdisk mode. It assumes you've read the basics of how to use Alpine local backup. The Raspberry Pi article contains information on how to install Alpine Linux on a Raspberry Pi.
Modem in full bridge mode
This particular page uses an example where you have a modem that uses PPPoE. You will need to modify the parts which do not apply to you.
In this example, I have a modem which has been configured in full bridge mode. PPP sessions are initiated on the router.
The modem I am using is a Cisco 877 Integrated Services Router. It has no web interface and is controlled over SSH. More information can be found Configuring a Cisco 877 in full bridge mode.
Network
/etc/hostname
Set this to your hostname eg:
<HOST_NAME>
/etc/hosts
Set your host and hostname
127.0.0.1 <HOST_NAME> <HOST_NAME>.<DOMAIN_NAME> ::1 <HOST_NAME> ipv6-gateway ipv6-loopback ff00::0 ipv6-localnet ff00::0 ipv6-mcastprefix ff02::1 ipv6-allnodes ff02::2 ipv6-allrouters ff02::3 ipv6-allhosts
/etc/network/interfaces
Configure your network interfaces. Change "yourISP" to the file name of the file in /etc/ppp/peers/yourISP
# # Network Interfaces # # Loopback interfaces auto lo iface lo inet loopback address 127.0.0.1 netmask 255.0.0.0 # Internal Interface - facing LAN auto eth0 iface eth0 inet static address 192.168.1.1 netmask 255.255.255.0 broadcast 192.168.1.255
PPP
Next you need to configure your router to be able to dial a PPP connection with the modem.
If your ISP uses PPP you may need to configure it. See PPP.
You will want to make sure you set your WAN interface, in this example we used eth1.
# External Interface - facing Modem allow-hotplug eth1 auto eth1 iface eth1 inet static address 192.168.0.2 netmask 255.255.255.252 broadcast 192.168.0.3 pre-up /sbin/ip link set eth1 up up ifup ppp0=yourISP down ifdown ppp0=yourISP post-down /sbin/ip link set eth1 up # Link to ISP iface yourISP inet ppp provider yourISP
IPoE
Alternatively, it's quite common for ISPs to use IPoE. IPoE is much simpler and runs DHCP only on the external interface. It should look something like:
# External interface to ISP
allow-hotplug eth1
auto eth1
iface eth1 inet dhcp
iface eth1 inet static
address 192.168.0.2
netmask 255.255.255.252
broadcast 192.168.0.3
iface eth1 inet6 manual
DHCP from ISP
Above we set DHCP and we set a static IP. This is so we can still forward packets through to the modem to be able to access the web interface or SSH.
We do still need DHCP to get an IP address from our ISP though. I like to use dhcpcd instead of udhcp (the default in Alpine Linux), because it allows for Prefix Delegation, which is used in IPv6 networks.
My /etc/dhcpcd.conf looks like this:
# Enable extra debugging
# debug
# logfile /var/log/dhcpcd.log
# Allow users of this group to interact with dhcpcd via the control
# socket.
#controlgroup wheel
# Inform the DHCP server of the hostname for DDNS.
hostname gateway
# Use the hardware address of the interface for the Client ID.
# clientid
# or
# Use the same DUID + IAID as set in DHCPv6 for DHCPv4 ClientID as
# per RFC4361. Some non-RFC compliant DHCP servers do not reply with
# this set. In this case, comment out duid and enable clientid above.
duid
# Persist interface configuration when dhcpcd exits.
persistent
# Rapid commit support.
# Safe to enable by default because it requires the equivalent option
# set on the server to actually work.
option rapid_commit
# A list of options to request from the DHCP server.
option domain_name_servers, domain_name, domain_search, host_name
option classless_static_routes
# Most distributions have NTP support.
option ntp_servers
# Respect the network MTU.
# Some interface drivers reset when changing the MTU so disabled by
# default.
#option interface_mtu 1586
# A ServerID is required by RFC2131.
require dhcp_server_identifier
# Generate Stable Private IPv6 Addresses instead of hardware based
# ones
slaac private
# A hook script is provided to lookup the hostname if not set by the
# DHCP server, but it should not be run by default.
nohook lookup-hostname
# Disable solicitations on all interfaces
noipv6rs
# Wait for IP before forking to background
waitip 6
# Don't touch DNS
nohook resolv.conf
allowinterfaces eth1 eth0.2
# Use the interface connected to WAN
interface eth1
waitip 4
noipv4ll
ipv6rs # enable routing solicitation get the default IPv6 route
iaid 1
ia_pd 1/::/56 eth0.2/2/64
timeout 30
interface eth0.2
ipv6only
Basic IPtables firewall with routing
This demonstrates how to set up basic routing with a permissive outgoing firewall. Incoming packets are blocked. The rest is commented in the rule set.
First install iptables:
apk add iptables ip6tables
######################################################################### # Basic iptables IPv4 routing rule set # # 192.168.1.0/24 routed directly to PPP0 via NAT # ######################################################################### # # Mangle Table # We leave this empty for the moment. # *mangle :PREROUTING ACCEPT [0:0] :INPUT ACCEPT [0:0] :FORWARD ACCEPT [0:0] :OUTPUT ACCEPT [0:0] :POSTROUTING ACCEPT [0:0] COMMIT # # Filter Table # This is where we decide to ACCEPT, DROP or REJECT packets # *filter :INPUT DROP [0:0] :FORWARD DROP [0:0] :OUTPUT ACCEPT [0:0] *filter # Create rule chain per input interface for forwarding packets :FWD_ETH0 - [0:0] :FWD_ETH1 - [0:0] :FWD_PPP0 - [0:0] # Create rule chain per input interface for input packets (for host itself) :IN_ETH0 - [0:0] :IN_ETH1 - [0:0] :IN_PPP0 - [0:0] # Create a log drop chain :LOG_DROP - [0:0] # Pass input packet to corresponding rule chain -A INPUT -i lo -j ACCEPT -A INPUT -i eth0 -j IN_ETH0 -A INPUT -i eth1 -j IN_ETH1 -A INPUT -i ppp0 -j IN_PPP0 # Pass forwarded packet to corresponding rule chain -A FORWARD -i eth0 -j FWD_ETH0 -A FORWARD -i eth1 -j FWD_ETH1 -A FORWARD -i ppp0 -j FWD_PPP0 # Forward LAN traffic out -A FWD_ETH0 -s 192.168.1.0/24 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Forward SSH packets from network to modem -A FWD_ETH1 -s 192.168.0.0/30 -d 192.168.1.0/24 -p tcp -m tcp --sport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Forward HTTP to modem's webserver -A FWD_ETH1 -s 192.168.0.0/30 -d 192.168.1.0/24 -p tcp -m tcp --sport 80 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Forward traffic to ISP -A FWD_PPP0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT # SSH to Router -A IN_ETH0 -s 192.168.1.0/24 -p tcp -m tcp --dport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # DNS to Router -A IN_ETH0 -s 192.168.1.0/24 -p tcp -m tcp --dport 1812 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # FreeRadius Client (eg a UniFi AP) -A IN_ETH0 -s 192.168.1.0/24 -p udp -m udp --dport 1812 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # NTP to Router -A IN_ETH0 -s 192.168.1.0/24 -p udp -m udp --dport 123 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Accept traffic -A IN_ETH0 -s 192.168.1.0/24 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # SSH To Modem from Router -A IN_ETH1 -s 192.168.0.1/32 -d 192.168.0.0/30 -p tcp -m tcp --sport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # HTTP to modem -A IN_ETH1 -s 192.168.0.1/32 -d 192.168.0.0/30 -p tcp -m tcp --sport 80 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Accept incoming tracked PPP0 connection -A IN_PPP0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT COMMIT # # NAT Table # This is where translation of packets happens as well as "forwarding" of ports # to specific hosts. # *nat :PREROUTING ACCEPT [0:0] :INPUT ACCEPT [0:0] :OUTPUT ACCEPT [0:0] :POSTROUTING ACCEPT [0:0] # Port forwarding for Bittorrent -A PREROUTING -i ppp0 -p tcp -m tcp --dport 6881:6889 -j DNAT --to-destination 192.168.1.20 -A PREROUTING -i ppp0 -p udp -m udp --dport 6881:6889 -j DNAT --to-destination 192.168.1.20 # Allows routing to our modem subnet so we can access the web interface or SSH -A POSTROUTING -s 192.168.1.0/24 -d 192.168.0.1/32 -o eth1 -p tcp -m tcp --dport 22 -j MASQUERADE -A POSTROUTING -s 192.168.1.0/24 -d 192.168.0.1/32 -o eth1 -p tcp -m tcp --dport 80 -j MASQUERADE # Allows hosts of the network to use the PPP tunnel -A POSTROUTING -s 192.168.1.0/24 -o ppp0 -j MASQUERADE COMMIT
I'd also highly suggest reading these resources if you are new to iptables:
- Frozen Tux Iptables-tutorial
- Words of wisdom for #netfilter
- Things You Should Know About Netfilter
- Towards the perfect ruleset
/etc/sysctl.d/local.conf
# Controls IP packet forwarding net.ipv4.ip_forward = 1 # Needed to use fwmark, only required if you want to set up the VPN subnet later in this article net.ipv4.conf.all.rp_filter = 2 # Disable IPv6 net.ipv6.conf.all.disable_ipv6 = 1 net.ipv6.conf.lo.disable_ipv6 = 1 net.ipv6.conf.default.disable_ipv6 = 1
Note IPv6 is disabled here if you want that see the other tutorial Linux Router with VPN on a Raspberry Pi (IPv6). You may also wish to look at ip-sysctl.txt to read about the other keys.
DHCP
apk add dhcp
/etc/conf.d/dhcpd
Specify the configuration file location, interface to run on, and that you want DHCPD to run in IPv4 mode.
# /etc/conf.d/dhcpd: config file for /etc/init.d/dhcpd # If you require more than one instance of dhcpd, you can create symbolic # links to dhcpd service like so # cd /etc/init.d # ln -s dhcpd dhcpd.foo # cd ../conf.d # cp dhcpd dhcpd.foo # Now you can edit dhcpd.foo and specify a different configuration file. # You'll also need to specify a pidfile in the dhcpd.conf file. # See the pid-file-name option in the dhcpd.conf man page for details. # If you wish to run dhcpd in a chroot environment, uncomment the following line # DHCPD_CHROOT="/var/lib/dhcp/chroot" # All file paths below are relative to the chroot. # You can specify a different chroot directory, but MAKE SURE it's empty. # Specify a configuration file - the default is /etc/dhcp/dhcpd.conf DHCPD_CONF="/etc/dhcp/dhcpd.conf" # Configure which interface or interfaces to for dhcpd to listen on. # List all interfaces space separated. If this is not specified then # we listen on all interfaces. DHCPD_IFACE="eth0" # Insert any other dhcpd options. See the man page for a full list. DHCPD_OPTS="-4"
/etc/dhcp/dhcpd.conf
Configure your DHCP configuration server. For my DHCP server I'm going to have three subnets. Each has a specific purpose. You may choose to have any number of subnets as shown below. The broadcast-address will be different if you used VLANs. However, in this case VLANs are not used.
authoritative;
ddns-update-style interim;
shared-network home {
subnet 192.168.1.0 netmask 255.255.255.0 {
range 192.168.1.10 192.168.1.240;
option subnet-mask 255.255.255.0;
option broadcast-address 192.168.1.255;
option routers 192.168.1.1;
option ntp-servers 192.168.1.1;
option domain-name-servers 192.168.1.1;
allow unknown-clients;
}
subnet 192.168.2.0 netmask 255.255.255.0 {
range 192.168.2.10 192.168.2.240;
option subnet-mask 255.255.255.0;
option broadcast-address 192.168.2.255;
option routers 192.168.2.1;
option ntp-servers 192.168.2.1;
option domain-name-servers 192.168.1.1;
ignore unknown-clients;
}
subnet 192.168.3.0 netmask 255.255.255.0 {
range 192.168.3.10 192.168.3.240;
option subnet-mask 255.255.255.0;
option broadcast-address 192.168.3.255;
option routers 192.168.3.1;
option ntp-servers 192.168.3.1;
option domain-name-servers 192.168.1.1;
ignore unknown-clients;
}
}
host Gaming_Computer {
hardware ethernet 00:53:00:FF:FF:11;
fixed-address 192.168.1.20;
option subnet-mask 255.255.255.0;
option broadcast-address 192.168.1.255;
option routers 192.168.1.1;
option host-name "gaming_computer";
}
host Linux_Workstation {
hardware ethernet 00:53:00:FF:FF:22;
fixed-address 192.168.2.21;
option subnet-mask 255.255.255.0;
option broadcast-address 192.168.2.255;
option routers 192.168.2.1;
option host-name "linux_workstation";
}
host printer {
hardware ethernet 00:53:00:FF:FF:33;
fixed-address 192.168.3.9;
option subnet-mask 255.255.255.0;
option broadcast-address 192.168.3.255;
option routers 192.168.3.1;
}
Make sure to add this to the default run level once configured:
rc-update add dhcpd default
Synchronizing the clock
You can choose to use BusyBox's ntpd or you can choose a more fully fledged option like OpenNTPD or Chrony
Busybox /etc/conf.d/ntpd
Allow clients to synchronize their clocks with the router.
# By default ntpd runs as a client. Add -l to run as a server on port 123. NTPD_OPTS="-l -N -p <REMOTE TIME SERVER>"
Make sure to add this to the default run level once configured:
rc-update add ntpd default
or if you prefer, to synchronize with multiple servers...
Chrony /etc/chrony.conf
apk add chrony
logdir /var/log/chrony log measurements statistics tracking allow 192.168.0.0/30 allow 192.168.1.0/24 allow 192.168.2.0/24 allow 192.168.3.0/24 allow 192.168.4.0/24 broadcast 30 192.168.0.3 broadcast 30 192.168.1.255 broadcast 30 192.168.2.255 broadcast 30 192.168.3.255 broadcast 30 192.168.4.255 server 0.pool.ntp.org iburst server 1.pool.ntp.org iburst server 2.pool.ntp.org iburst server 3.pool.ntp.org iburst initstepslew 10 pool.ntp.org driftfile /var/lib/chrony/chrony.drift hwclockfile /etc/adjtime rtcdevice /dev/rtc0 rtcsync
OpenNTPD /etc/ntpd.conf
Install OpenNTPD
apk add openntpd
Add to default run level.
rc-update add openntpd default
/etc/ntpd.conf
# sample ntpd configuration file, see ntpd.conf(5) # Addresses to listen on (ntpd does not listen by default) listen on 192.168.1.1 listen on 192.168.2.1 # sync to a single server #server ntp.example.org # use a random selection of NTP Pool Time Servers # see http://support.ntp.org/bin/view/Servers/NTPPoolServers server 0.pool.ntp.org server 1.pool.ntp.org server 2.pool.ntp.org server 3.pool.ntp.org
tlsdate
The time can also be extracted from a https handshake. If the certificate is self-signed you will need to use skip-verification:
apk add tlsdate
tlsdate -V --skip-verification -p 80 -H example.com
timezone
You might also want to set a timezone, see Setting the timezone.
Saving Time
There are two ways to do this. If you didn't buy an RTC, see Saving time with Software Clock. If you did, like the PiFace Real Time Clock, see Saving time with Hardware Clock
Unbound DNS forwarder with dnscrypt
We want to be able to do lookups using dnscrypt without installing DNSCrypt on every client on the network. DNSCrypt can use it's own protocol or DNS over HTTPS.
The router will also run a DNS forwarder and request unknown domains over DNSCrypt for our clients. Borrowed from the ArchLinux wiki article on dnscrypt-proxy.
Unbound
First install
apk add unbound
/etc/unbound/unbound.conf
server:
# Use this to include other text into the file.
include: "/etc/unbound/filter.conf"
# verbosity number, 0 is least verbose. 1 is default.
verbosity: 1
# specify the interfaces to answer queries from by ip-address.
# The default is to listen to localhost (127.0.0.1 and ::1).
# specify 0.0.0.0 and ::0 to bind to all available interfaces.
# specify every interface[@port] on a new 'interface:' labelled line.
# The listen interfaces are not changed on reload, only on restart.
interface: 192.168.2.1
interface: 192.168.3.1
# Enable IPv4, "yes" or "no".
do-ip4: yes
# Enable IPv6, "yes" or "no".
do-ip6: yes
# Enable UDP, "yes" or "no".
do-udp: yes
# Enable TCP, "yes" or "no".
do-tcp: yes
# control which clients are allowed to make (recursive) queries
# to this server. Specify classless netblocks with /size and action.
# By default everything is refused, except for localhost.
# Choose deny (drop message), refuse (polite error reply),
# allow (recursive ok), allow_setrd (recursive ok, rd bit is forced on),
# allow_snoop (recursive and nonrecursive ok)
# deny_non_local (drop queries unless can be answered from local-data)
# refuse_non_local (like deny_non_local but polite error reply).
# access-control: 0.0.0.0/0 refuse
# access-control: 127.0.0.0/8 allow
# access-control: ::0/0 refuse
# access-control: ::1 allow
# access-control: ::ffff:127.0.0.1 allow
access-control: 192.168.1.0/24 allow
access-control: 192.168.2.0/24 allow
access-control: 192.168.3.0/24 allow
# the log file, "" means log to stderr.
# Use of this option sets use-syslog to "no".
logfile: "/var/log/unbound/unbound.log"
# Log to syslog(3) if yes. The log facility LOG_DAEMON is used to
# log to. If yes, it overrides the logfile.
use-syslog: no
# print one line with time, IP, name, type, class for every query.
# log-queries: no
# print one line per reply, with time, IP, name, type, class, rcode,
# timetoresolve, fromcache and responsesize.
# log-replies: no
# enable to not answer id.server and hostname.bind queries.
hide-identity: yes
# enable to not answer version.server and version.bind queries.
# hide-version: yes
# enable to not answer trustanchor.unbound queries.
hide-trustanchor: yes
# Harden against very small EDNS buffer sizes.
harden-short-bufsize: yes
# Harden against unseemly large queries.
harden-large-queries: yes
# Harden against out of zone rrsets, to avoid spoofing attempts.
harden-glue: yes
# Harden against receiving dnssec-stripped data. If you turn it
# off, failing to validate dnskey data for a trustanchor will
# trigger insecure mode for that zone (like without a trustanchor).
# Default on, which insists on dnssec data for trust-anchored zones.
harden-dnssec-stripped: yes
# Harden against queries that fall under dnssec-signed nxdomain names.
harden-below-nxdomain: yes
# Harden the referral path by performing additional queries for
# infrastructure data. Validates the replies (if possible).
# Default off, because the lookups burden the server. Experimental
# implementation of draft-wijngaards-dnsext-resolver-side-mitigation.
# harden-referral-path: no
# Harden against algorithm downgrade when multiple algorithms are
# advertised in the DS record. If no, allows the weakest algorithm
# to validate the zone.
harden-algo-downgrade: yes
# Use 0x20-encoded random bits in the query to foil spoof attempts.
# This feature is an experimental implementation of draft dns-0x20.
use-caps-for-id: yes
# Allow the domain (and its subdomains) to contain private addresses.
# local-data statements are allowed to contain private addresses too.
private-domain: "<HOSTNAME>"
# if yes, the above default do-not-query-address entries are present.
# if no, localhost can be queried (for testing and debugging).
do-not-query-localhost: no
# File with trusted keys, kept uptodate using RFC5011 probes,
# initial file like trust-anchor-file, then it stores metadata.
# Use several entries, one per domain name, to track multiple zones.
#
# If you want to perform DNSSEC validation, run unbound-anchor before
# you start unbound (i.e. in the system boot scripts). And enable:
# Please note usage of unbound-anchor root anchor is at your own risk
# and under the terms of our LICENSE (see that file in the source).
# auto-trust-anchor-file: "@UNBOUND_ROOTKEY_FILE@"
auto-trust-anchor-file: "/etc/unbound/root.key"
# If unbound is running service for the local host, then it is useful
# to perform lan-wide lookups to the upstream, and unblock the
# long list of local-zones above. If this unbound is a dns server
# for a network of computers, disabled is better and stops information
# leakage of local lan information.
unblock-lan-zones: no
# If you configure local-data without specifying local-zone, by
# default, a transparent local-zone is created for the data.
#
# You can add locally served data with
# local-zone: "local." static
# local-data: "mycomputer.local. IN A 192.0.2.51"
# local-data: 'mytext.local TXT "content of text record"'
# request upstream over TLS (with plain DNS inside the TLS stream).
# Default is no. Can be turned on and off with unbound-control.
# tls-upstream: no
# Forward zones
# Create entries like below, to make all queries for 'example.com' and
# 'example.org' go to the given list of servers. These servers have to handle
# recursion to other nameservers. List zero or more nameservers by hostname
# or by ipaddress. Use an entry with name "." to forward all queries.
# If you enable forward-first, it attempts without the forward if it fails.
# forward-zone:
# name: "example.com"
# forward-addr: 192.0.2.68
# forward-addr: 192.0.2.73@5355 # forward to port 5355.
# forward-first: no
# forward-tls-upstream: no
# forward-no-cache: no
# forward-zone:
# name: "example.org"
# forward-host: fwd.example.com
forward-zone:
name: "."
forward-addr: 172.16.32.1@53
forward-addr: ::1@53000
forward-addr: 127.0.0.1@53000
Additional DNS level filtering
This script takes in a list of domains and produces a filter file. We are directing all lookups to "0.0.0.1" which is an invalid IP and should fail immediately, unlike localhost.
/etc/unbound/unbound.conf
In your main unbound configuration, add
include: /etc/unbound/filter.conf
Script to prepare/sort domains for Unbound
#!/bin/sh
##################################################
# Script taken from http://npr.me.uk/unbound.html
# Note: you need GNU sed
##################################################
# Remove "#" comments
# Remove space and tab
# Remove blank lines
# Remove localhost and broadcasthost lines
# Keep just the hosts
# Remove leading and trailing space and tab (again)
# Make everything lower case
sed -e "s/#.*//" \
-e "s/[ \x09]*$//"\
-e "/^$/ d" \
-e "/^.*local.*/ d" \
-e "/^.*broadcasthost.*/ d" \
-e "s/\(^.*\) \([a-zA-Z0-9\.\-]*\)/\2/" \
-e "s/^[ \x09]*//;s/[ \x09]*$//" $1 \
-e "s/\(.*\)/\L\1/" hosts.txt > temp1.txt
# Remove any duplicate hosts
sort temp1.txt | uniq >temp2.txt
# Remove any hosts starting with "."
# Create the two required lines for each host.
sed -e "/^\..*/ d" \
-e "s/\(^.*\)/local-zone: \x22\1\x22 redirect\nlocal-data: \x22\1 A 0.0.0.1\x22/" \
temp2.txt > filter.conf
# Clean up
rm temp1.txt
rm temp2.txt
DNSCrypt
You can test that you're not getting DNS leaks by using dnsleak.com or this one from GRC. Providers like CloudFlare and Google (1.1.1.1, 8.8.8.8) use anycast which should be pointing to a server located to where your VPN exits.
/etc/dnscrypt-proxy/dnscrypt-proxy.toml
Using the sample dnscrypt config is fine. You'll need to make these changes:
listen_addresses = ['127.0.0.1:53000', '[::1]:53000']
Add policy route for dnscrypt over VPN
Add a policy based route based on the uid of the dnscrypt user. On Alpine Linux dnscrypt-proxy runs as a specific user so check /etc/passwd
dnscrypt:x:103:104:dnscrypt:/var/empty:/sbin/nologin
In this example, the dnscrypt user has the uid 103.

Add this to fwmark_rules eg:
/etc/network/fwmark_rules
# Route DNSCrypt user through the VPN table /sbin/ip rule add uidrange 103-103 table VPN prio 200
rc-update add unbound default
rc-update add dnscrypt-proxy default
Random number generation
There are two ways to assist with random number generation Entropy and randomness. This can be particularly useful if you're generating your own Diffie-Hellman nonce file, used in the FreeRadius EAP-TLS configuration section, or any process such as generating certificates or public private keys.
Haveged
Haveged is a great way to improve random number generation speed. It uses the unpredictable random number generator based upon an adaptation of the HAVEGE algorithm.
Install haveged:
apk add haveged
Start haveged service:
service haveged start
Add service to boot
rc-update add haveged default
Start rngd service:
service haveged start
Add service to boot:
rc-update add haveged default
rng-tools with bcm2708-rng
Pre Alpine Linux 3.8 (which includes rngd 5)
All Raspberry Pis come with the bcm2708-rng random number generator on board. If you are doing this project on a Raspberry Pi then you may choose to use that.
Add the kernel module to /etc/modules:
echo "bcm2708-rng" > /etc/modules
Insert module:
modprobe bcm2708-rng
Install rng-tools:
apk add rng-tools
Set the random device (/dev/random) and rng device (/dev/hwrng) in /etc/conf.d/rngd
RNGD_OPTS="--no-drng=1 --no-tpm=1 -o /dev/random -r /dev/hwrng"
Post Alpine Linux 3.8 (which includes rngd 6)
With AlpineLinux 3.8 you don't have to insert the module as it is built in the kernel.
Additionally, the syntax has changed for rngd so for /etc/conf.d/rngd you'll need
RNGD_OPTS="-x1 -o /dev/random -r /dev/hwrng"
Start rngd service:
service rngd start
Add service to boot:
rc-update add rngd default
You can test it with:
cat /dev/hwrng | rngtest -c 1000
You should see something like:
rngtest 5 Copyright (c) 2004 by Henrique de Moraes Holschuh This is free software; see the source for copying conditions. There is NO warranty; not even for MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. rngtest: starting FIPS tests... rngtest: bits received from input: 20000032 rngtest: FIPS 140-2 successes: 1000 rngtest: FIPS 140-2 failures: 0 rngtest: FIPS 140-2(2001-10-10) Monobit: 0 rngtest: FIPS 140-2(2001-10-10) Poker: 0 rngtest: FIPS 140-2(2001-10-10) Runs: 0 rngtest: FIPS 140-2(2001-10-10) Long run: 0 rngtest: FIPS 140-2(2001-10-10) Continuous run: 0 rngtest: input channel speed: (min=117.709; avg=808.831; max=3255208.333)Kibits/s rngtest: FIPS tests speed: (min=17.199; avg=22.207; max=22.653)Mibits/s rngtest: Program run time: 25178079 microseconds
It's possible you might have a some failures. That's okay, two runs I did previously had a failure each.
WiFi 802.1x EAP and FreeRadius
A more secure way than using pre-shared keys (WPA2) is to use EAP-TLS and use separate certificates for each device. See FreeRadius EAP-TLS configuration
VPN Tunnel on specific subnet
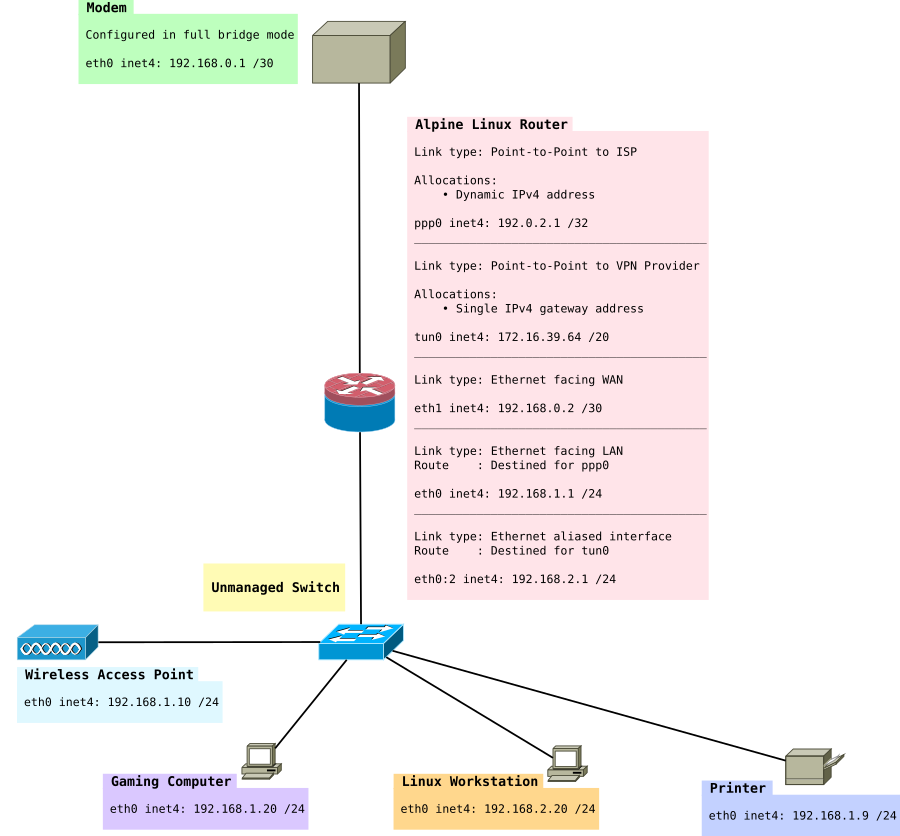
As mentioned earlier in this article, it might be useful to have a VPN subnet and a non-VPN subnet. Typically, gaming consoles or computers might want low-latency connections. For this exercise we use fwmark.
We expand the network to look like this:
Install the necessary packages:
apk add openvpn iproute2 iputils
/etc/modules
You'll want to add the tun module
tun
/etc/iproute2/rt_tables
Add the two routing tables to the bottom of rt_tables. It should look something like this:
# # reserved values # 255 local 254 main 253 default 0 unspec # # local # #1 inr.ruhep 1 ISP 2 VPN
/etc/network/interfaces
Next, add the virtual interface (really just a IP address to eth0) eth0:2, just under eth0 will do.
# Route to VPN subnet auto eth0:2 iface eth0:2 inet static address 192.168.2.1 netmask 255.255.255.0 broadcast 192.168.2.255 post-up /etc/network/fwmark_rules
/etc/sysctl.d/local.conf
If you want to use fwmark rules you need to change this setting. It causes the router to still do source validation.
# Needed to use fwmark net.ipv4.conf.all.rp_filter = 2
fwmark won't work if you have this set to 1.
/etc/network/fwmark_rules
In this file, we want to put the fwmark rules and set the correct priorities.
#!/bin/sh # Normal packets to go direct out WAN /sbin/ip rule add fwmark 1 table ISP prio 100 # Put packets destined into VPN when VPN is up /sbin/ip rule add fwmark 2 table VPN prio 200 # Prevent packets from being routed out when VPN is down. # This prevents packets from falling back to the main table # that has a priority of 32766 /sbin/ip rule add prohibit fwmark 2 prio 300
/etc/ppp/ip-up
Next, we want to create the routes that should be run when PPP comes online. There are special hooks we can use in ip-up and ip-down to refer to the IP address, ppp man file - Scripts You can also read about them in your man file if you have ppp-doc installed.
#!/bin/sh
#
# This script is run by pppd when there's a successful ppp connection.
#
# Flush out any old rules that might be there
/sbin/ip route flush table ISP
# Add route to table from subnets on LAN
/sbin/ip route add 192.168.1.0/24 dev eth0 table ISP
/sbin/ip route add 192.168.2.0/24 dev eth0 table ISP
# Add route from IP given by ISP to the table
/sbin/ip rule add from ${IPREMOTE} table ISP prio 100
# Add a default route
/sbin/ip route add table ISP default via ${IPREMOTE} dev ${IFNAME}
/etc/ppp/ip-down
#!/bin/sh
#
# This script is run by pppd after the connection has ended.
#
# Delete the rules when we take the interface down
/sbin/ip rule del from ${IPREMOTE} table ISP prio 100
/etc/openvpn/route-up-fwmark.sh
OpenVPN needs similar routing scripts and it also has it's own special hooks that allow you to specify particular values. A full list is here OpenVPN man file - Environmental Variables
#!/bin/sh
#
# This script is run by OpenVPN when there's a successful VPN connection.
#
# Flush out any old rules that might be there
/sbin/ip route flush table VPN
# Add route to table from 192.168.2.0/24 subnet on LAN
/sbin/ip route add 192.168.2.0/24 dev eth0 table VPN
# Add route from VPN interface IP to the VPN table
/sbin/ip rule add from ${ifconfig_local} table VPN prio 200
# Add a default route
/sbin/ip route add default via ${ifconfig_local} dev ${dev} table VPN
/etc/openvpn/route-pre-down-fwmark.sh
#!/bin/sh
#
# This script is run by OpenVPN after the connection has ended
#
# Delete the rules when we take the interface down
/sbin/ip rule del from ${ifconfig_local} table VPN prio 200
What I found was when starting and stopping the OpenVPN service if you used:
service openvpn stop
The rules in route-pre-down-fwmark.sh were not executed.
However:
/etc/init.d/openvpn stop
seemed to work correctly.
Advanced IPtables rules that allow us to route into our two routing tables
This is an expansion of the previous set of rules. It sets up NAT masquerading for the 192.168.2.0 to go through the VPN using marked packets.
I used these guides to write complete this:
- Conning the Mark: Multiwan connections using IPTables, MARK, CONNMARK and iproute2
- Multiwan connections addendum
- Netfilter packet flow
######################################################################### # Advanced routing rule set # Uses 192.168.1.0 via ISP # 192.168.2.0 via VPN # # Packets to/from 192.168.1.0/24 are marked with 0x1 and routed to ISP # Packets to/from 192.168.2.0/24 are marked with 0x2 and routed to VPN # ######################################################################### # # NAT Table # This is where translation of packets happens and "forwarding" of ports # to specific hosts. # *nat # Set default policies for table :PREROUTING ACCEPT [0:0] :INPUT ACCEPT [0:0] :OUTPUT ACCEPT [0:0] :POSTROUTING ACCEPT [0:0] # Port forwarding for Bittorrent -A PREROUTING -i tun0 -p tcp -m tcp --dport 6881:6889 -j DNAT --to-destination 192.168.2.20 -A PREROUTING -i tun0 -p udp -m udp --dport 6881:6889 -j DNAT --to-destination 192.168.2.20 # Allows routing to our modem subnet so we can access the web interface -A POSTROUTING -s 192.168.1.0/24 -d 192.168.0.1/32 -o eth1 -p tcp -m tcp --dport 80 -j MASQUERADE -A POSTROUTING -s 192.168.2.0/24 -d 192.168.0.1/32 -o eth1 -p tcp -m tcp --dport 80 -j MASQUERADE # Allows hosts of the network to use the VPN tunnel -A POSTROUTING -o tun0 -j MASQUERADE # Allows hosts of the network to use the PPP tunnel -A POSTROUTING -o ppp0 -j MASQUERADE COMMIT # # Filter Table # This is where we decide to ACCEPT, DROP or REJECT things # *filter :INPUT DROP [0:0] :FORWARD DROP [0:0] :OUTPUT ACCEPT [0:0] # Create rule chain per input interface for forwarding packets :FWD_ETH0 - [0:0] :FWD_ETH1 - [0:0] :FWD_PPP0 - [0:0] :FWD_TUN0 - [0:0] # Create rule chain per input interface for input packets (for host itself) :IN_ETH0 - [0:0] :IN_ETH1 - [0:0] :IN_PPP0 - [0:0] :IN_TUN0 - [0:0] # Create a log drop chain :LOG_DROP - [0:0] # Create a reject chain :LOG_REJECT - [0:0] # Pass input packet to corresponding rule chain -A INPUT -i lo -j ACCEPT -A INPUT -i eth0 -j IN_ETH0 -A INPUT -i eth1 -j IN_ETH1 -A INPUT -i ppp0 -j IN_PPP0 -A INPUT -i tun0 -j IN_TUN0 # Track forwarded packets -A FORWARD -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT # Pass forwarded packet to corresponding rule chain -A FORWARD -i eth0 -j FWD_ETH0 -A FORWARD -i eth1 -j FWD_ETH1 -A FORWARD -i ppp0 -j FWD_PPP0 -A FORWARD -i tun0 -j FWD_TUN0 # Forward traffic to ISP -A FWD_ETH0 -s 192.168.1.0/24 -j ACCEPT # Forward traffic to VPN -A FWD_ETH0 -s 192.168.2.0/24 -j ACCEPT # Allow excepted server to be FORWARD to ppp0 #-A FWD_ETH0 -s 192.168.2.0/24 -d <IP_OF_EXCEPTED_SERVER>/32 -o ppp0 -j ACCEPT # Forward SSH packets from network to modem -A FWD_ETH1 -s 192.168.0.1/32 -d 192.168.1.0/24 -p tcp -m tcp --sport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A FWD_ETH1 -s 192.168.0.1/32 -d 192.168.2.0/24 -p tcp -m tcp --sport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Forward HTTP packets from network to modem -A FWD_ETH1 -s 192.168.0.1/32 -d 192.168.1.0/24 -p tcp -m tcp --sport 80 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A FWD_ETH1 -s 192.168.0.1/32 -d 192.168.2.0/24 -p tcp -m tcp --sport 80 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Forward Bittorrent Port to workstation -A FWD_TUN0 -d 192.168.2.20/32 -p tcp -m tcp --dport 6881:6889 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A FWD_TUN0 -d 192.168.2.20/32 -p udp -m udp --dport 6881:6889 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # SSH to Router -A IN_ETH0 -s 192.168.1.0/24 -p tcp -m tcp --dport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A IN_ETH0 -s 192.168.2.0/24 -p tcp -m tcp --dport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # DNS to Router -A IN_ETH0 -s 192.168.1.0/24 -p udp -m udp --dport 53 -m conntrack --ctstate NEW -j ACCEPT -A IN_ETH0 -s 192.168.2.0/24 -p udp -m udp --dport 53 -m conntrack --ctstate NEW -j ACCEPT # FreeRadius Client (eg a UniFi AP) -A IN_ETH0 -s 192.168.1.0/24 -p tcp -m tcp --dport 1812 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A IN_ETH0 -s 192.168.1.0/24 -p udp -m udp --dport 1812 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Ubiquiti UAP Device Discovery Broadcast -A IN_ETH0 -s 192.168.1.0/24 -p udp -m udp --dport 10001 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # NTP to Router -A IN_ETH0 -s 192.168.1.0/24 -p udp -m udp --dport 123 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A IN_ETH0 -s 192.168.2.0/24 -p udp -m udp --dport 123 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Accept traffic to router on both subnets -A IN_ETH0 -s 192.168.1.0/24 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A IN_ETH0 -s 192.168.2.0/24 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Allow excepted server to be INPUT to eth0 from LAN #-A IN_ETH0 -s 192.168.2.0/24 -d <IP_OF_EXCEPTED_SERVER>/32 -o ppp0 -j ACCEPT # SSH To Modem from Router -A IN_ETH1 -s 192.168.0.1/32 -d 192.168.0.0/30 -p tcp -m tcp --sport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # HTTP To Modem from Router -A IN_ETH1 -s 192.168.0.1/32 -d 192.168.0.0/30 -p tcp -m tcp --sport 80 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Accept incoming tracked PPP0 connection -A IN_PPP0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT # Log dropped packets coming in on PPP0 -A IN_PPP0 -j LOG --log-prefix "DROP:INPUT " --log-level 6 -A IN_PPP0 -j LOG_DROP # Accept incoming tracked TUN0 connection -A IN_TUN0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT # Log dropped packets coming in on TUN0 -A IN_TUN0 -j LOG --log-prefix "DROP:INPUT " --log-level 6 -A IN_TUN0 -j LOG_DROP COMMIT # # Mangle Table # This is the place where our markings happen, whether they be 0x1 or 0x2 # *mangle # Set default policies for table :PREROUTING ACCEPT [0:0] :INPUT ACCEPT [0:0] :FORWARD ACCEPT [0:0] :OUTPUT ACCEPT [0:0] :POSTROUTING ACCEPT [0:0] # Restore CONNMARK to the MARK (If one doesn't exist then no mark is set) -A PREROUTING -j CONNMARK --restore-mark --nfmask 0xffffffff --ctmask 0xffffffff # If packet MARK is 2, then it means there is already a connection mark and the # original packet came in on VPN -A PREROUTING -s 192.168.2.0/24 -m mark --mark 0x2 -j ACCEPT # Check exception (this is a server which when accessed on a 192.168.2.0/24 address will go out the ISP table) are 0x1 #-A PREROUTING -s 192.168.2.0/24 -d <IP_OF_EXCEPTED_SERVER>/32 -m mark --mark 0x1 -j ACCEPT # Mark packets coming from 192.168.2.0/24 are 0x2 -A PREROUTING -s 192.168.2.0/24 -j MARK --set-xmark 0x2/0xffffffff # If packet MARK is 1, then it means there is already a connection mark and the # original packet came in on ISP -A PREROUTING -s 192.168.1.0/24 -m mark --mark 0x1 -j ACCEPT # Mark packets 192.168.1.0/24 are 0x1 -A PREROUTING -s 192.168.1.0/24 -j MARK --set-xmark 0x1/0xffffffff # Mark exception (this is a server which when accessed on a 192.168.2.0/24 address will go out the ISP table) as 0x1 #-A PREROUTING -s 192.168.2.0/24 -d <IP_OF_EXCEPTED_SERVER>/32 -j MARK --set-xmark 0x1/0xffffffff # Set mark to 0 - This is for the modem. Otherwise it will mark with 0x1 or 0x2 -A PREROUTING -d 192.168.0.1/32 -j MARK --set-xmark 0x0/0xffffffff # Save MARK to CONNMARK (remember iproute can't see CONNMARKs) -A PREROUTING -j CONNMARK --save-mark --nfmask 0xffffffff --ctmask 0xffffffff COMMIT
You may want to delete certain rules here that do not apply to you, e.g. the FreeRadius rules. That is covered later in this article.
OpenVPN Routing
Usually when you connect with OpenVPN, the remote VPN server will push routes down to your system. We don't want this as we still want to be able to access the internet without the VPN. We have also created our own routes that we want to use earlier in this guide.
You'll need to add this to the bottom of your OpenVPN configuration file:
# Prevents default gateway from being set on the default routing table route-noexec # Allows route-up script to be executed script-security 2 # Calls custom shell script after connection to add necessary routes route-up /etc/openvpn/route-up-fwmark.sh route-pre-down /etc/openvpn/route-pre-down-fwmark.sh
My VPNs are arranged like this in /etc/openvpn:
OpenVPN configuration file for that server:
countrycode.serverNumber.openvpn.conf
OpenVPN certs for that server:
countrycode.serverNumber.openvpn/countrycode.serverNumber.openvpn.crt countrycode.serverNumber.openvpn/countrycode.serverNumber.openvpn.key countrycode.serverNumber.openvpn/myKey.crt countrycode.serverNumber.openvpn/myKey.key
So I use this helpful script to automate the process of changing between servers:
#!/bin/sh
vpn_server_filename=$1
rm /etc/openvpn/openvpn.conf
ln -s $vpn_server_filename /etc/openvpn/openvpn.conf
chown -R openvpn:openvpn /etc/openvpn
chmod -R a=-rwx,u=+rX /etc/openvpn
chmod u=x /etc/openvpn/*.sh*
if grep -Fxq "#CustomStuffHere" openvpn.conf
then
echo "Not adding custom routes, this server has been used previously"
else
echo "Adding custom route rules"
cat <<EOF >> /etc/openvpn/openvpn.conf
#CustomStuffHere
# Prevents default gateway from being set on the default routing table
route-noexec
# Allows route-up script to be executed
script-security 2
# Calls custom shell script after connection to add necessary routes
route-up /etc/openvpn/route-up-fwmark.sh
route-pre-down /etc/openvpn/route-pre-down-fwmark.sh
# Logging of OpenVPN to file
#log /etc/openvpn/openvpn.log
EOF
fi
echo "Remember to set BitTorrent port forward in VPN control panel"
That way I can simply change between servers by running:
changevpn.sh countrycode.serverNumber.openvpn
and then restart openvpn. I am also reminded to put the port forward through on the VPN control panel so my BitTorrent client is connectable:
service openvpn restart
Finally add openvpn to the default run level
rc-update add openvpn default
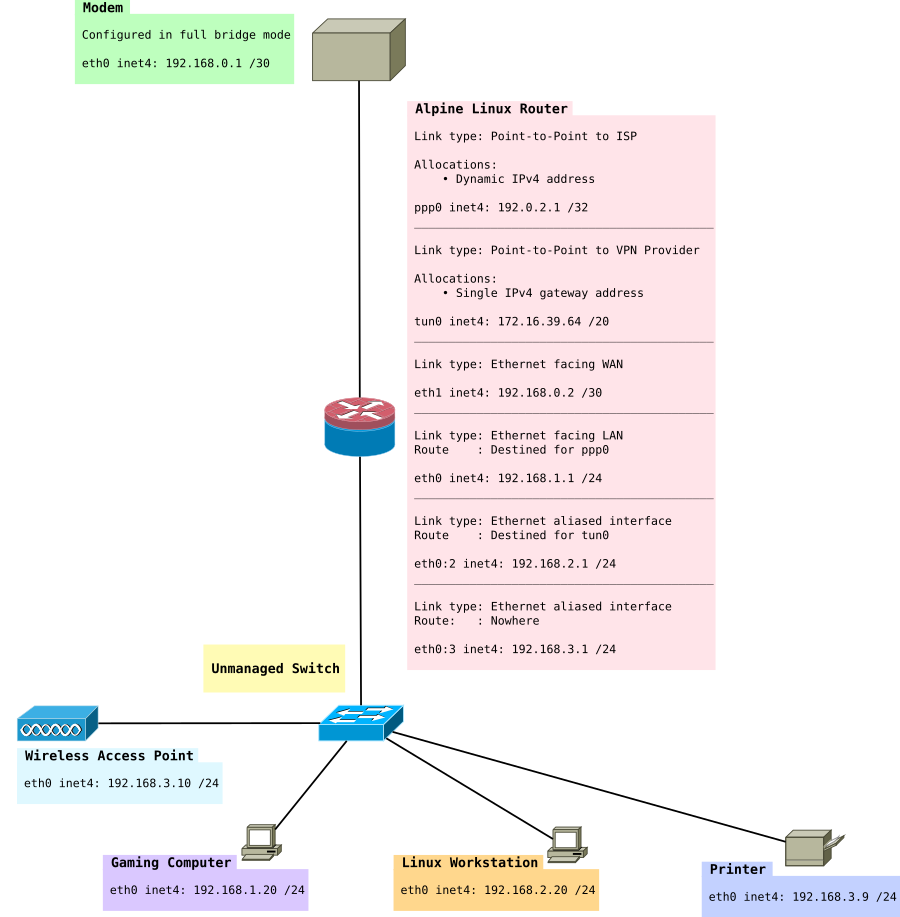
Creating a LAN only Subnet
In this section, we'll be creating a LAN only subnet. This subnet will be 192.168.3.0/24. The idea of this subnet is nodes in it cannot have their packets forwarded to the Internet, however they can be accessed via the other LAN subnets 192.168.1.0/24 and 192.168.2.0/24. This approach doesn't use VLANs although that would be recommended if you had a managed switch. The idea of this subnet is for things like WiFi access points, IP Phones which contact a local Asterisk server and of course printers.
At the end of this section we will have something like:
/etc/iproute2/rt_tables
First we'll add a third routing table:
3 LAN
/etc/network/interfaces
Add a an extra virtual interface (really just a IP address to eth0).
# LAN Only auto eth0:3 iface eth0:3 inet static address 192.168.3.1 netmask 255.255.255.0 broadcast 192.168.3.255 post-up /etc/network/route_LAN
/etc/network/route_LAN
This file will have our route added to it
#!/bin/sh # Add routes from ISP to LAN /sbin/ip route add 192.168.1.0/24 dev eth0 table LAN # Add route from VPN to LAN /sbin/ip route add 192.168.2.0/24 dev eth0 table LAN # Add route from LAN to it's own table /sbin/ip route add 192.168.3.0/24 dev eth0 table LAN
/etc/ppp/ip-up
Append a route from the LAN subnet to the ISP table
# Add route to LAN subnet /sbin/ip route add 192.168.3.0/24 dev eth0 table ISP
/etc/openvpn/route-up-fwmark.sh
Append a route from the LAN subnet to the VPN table
# Add route to LAN only subnet /sbin/ip route add 192.168.3.0/24 dev eth0 table VPN
/etc/ntpd.conf
Add a listen address for ntp (OpenNTPD).
You should now have:
# Addresses to listen on (ntpd does not listen by default) listen on 192.168.1.1 listen on 192.168.2.1 listen on 192.168.3.1
Devices needing the correct time will need to use this NTP server because they will not be able to get it from the Internet.
Blocking bogons
Our LAN now has 4 subnets in total that are possible:
- 192.168.0.0/30 (connection between modem and router)
- 192.168.1.0/24 (ISP table, directly routed out WAN)
- 192.168.2.0/24 (VPN table, routed out VPN)
- 192.168.3.0/24 (Null routed subnet for LAN only hosts)
- 172.16.32.0/20 (VPN provider's network, so we can access things on the VPN's network).
Everything else should be rejected. No packets should ever be forwarded on 192.168.5.2 or 10.0.0.5 for example.
Installing ipset
Install ipset:
apk add ipset
Add it to start up:
rc-update add ipset default
Now we need to load the lists of addresses into ipset Securing Your Server using IPset and Dynamic Blocklists mentions a script which was particularly useful. This script could be run on a cron job if you wanted to regularly update it and for the full bogon list you should as they change when that address space has been allocated.
For the purpose of this we will be using just the bogon-bn-nonagg.txt list.
0.0.0.0/8 10.0.0.0/8 100.64.0.0/10 127.0.0.0/8 169.254.0.0/16 172.16.0.0/12 192.0.0.0/24 192.0.2.0/24 192.168.0.0/16 198.18.0.0/15 198.51.100.0/24 203.0.113.0/24 224.0.0.0/4 240.0.0.0/4
This is unlikely to change as it's the IPV4 Reserved IP addresses space. The script:
#! /bin/bash
# /usr/local/sbin/fullbogons-ipv4
# BoneKracker
# Rev. 11 October 2012
# Tested with ipset 6.13
# Purpose: Periodically update an ipset used in a running firewall to block
# bogons. Bogons are addresses that nobody should be using on the public
# Internet because they are either private, not to be assigned, or have
# not yet been assigned.
#
# Notes: Call this from crontab. Feed updated every 4 hours.
# target="http://www.team-cymru.org/Services/Bogons/fullbogons-ipv4.txt"
# Use alternative URL from pfSense, due to 404 error with URL above
target="https://files.pfsense.org/lists/bogon-bn-nonagg.txt"
ipset_params="hash:net"
filename=$(basename ${target})
firewall_ipset=${filename%.*} # ipset will be filename minus ext
data_dir="/var/tmp/${firewall_ipset}" # data directory will be same
data_file="${data_dir}/${filename}"
# if data directory does not exist, create it
mkdir -pm 0750 ${data_dir}
# function to get modification time of the file in log-friendly format
get_timestamp() {
date -r $1 +%m/%d' '%R
}
# file modification time on server is preserved during wget download
[ -w ${data_file} ] && old_timestamp=$(get_timestamp ${data_file})
# fetch file only if newer than the version we already have
wget -qNP ${data_dir} ${target}
if [ "$?" -ne "0" ]; then
logger -p cron.err "IPSet: ${firewall_ipset} wget failed."
exit 1
fi
timestamp=$(get_timestamp ${data_file})
# compare timestamps because wget returns success even if no newer file
if [ "${timestamp}" != "${old_timestamp}" ]; then
temp_ipset="${firewall_ipset}_temp"
ipset create ${temp_ipset} ${ipset_params}
#sed -i '/^#/d' ${data_file} # strip comments
sed -ri '/^[#< \t]|^$/d' ${data_file} # occasionally the file has been xhtml
while read network; do
ipset add ${temp_ipset} ${network}
done < ${data_file}
# if ipset does not exist, create it
ipset create -exist ${firewall_ipset} ${ipset_params}
# swap the temp ipset for the live one
ipset swap ${temp_ipset} ${firewall_ipset}
ipset destroy ${temp_ipset}
# log the file modification time for use in minimizing lag in cron schedule
logger -p cron.notice "IPSet: ${firewall_ipset} updated (as of: ${timestamp})."
fi
Now you should see the list loaded into memory when you do:
ipset list
We want to save it so our router can refer to it next time it starts up. To do that:
/etc/init.d/ipset save
Adding our allowed networks
IPv4
ipset create allowed-nets-ipv4 hash:net,iface family inet
Then you can add each of your allowed networks:
ipset add allowed-nets-ipv4 192.168.0.0/30,eth1 ipset add allowed-nets-ipv4 192.168.1.0/24,eth0 ipset add allowed-nets-ipv4 192.168.2.0/24,eth0 ipset add allowed-nets-ipv4 192.168.3.0/24,eth0 ipset add allowed-nets-ipv4 127.0.0.0/8,lo ipset add allowed-nets-ipv4 172.16.32.0/20,tun0
IPv6
For IPv6, if you've got any Unique local address ranges you may choose to add them:
ipset create allowed-nets-ipv6 hash:net,iface family inet6
ipset add allowed-nets-ipv6 fde4:8dba:82e1::/48,tun0 ipset add allowed-nets-ipv6 fde4:8dba:82e1:ffff::/64,eth0
Finally, save the sets with this command so they can be loaded at the next boot:
/etc/init.d/ipset save
Restricting our LAN subnet with iptables, and blocking the bogons
Finally, we can apply our iptables rules, to filter both 192.168.3.0/24 and make sure that subnets like 192.168.5.0/24 are not forwarded or accessible by our router. You will need to review these rules, and remove the ones that do not apply to you.
Don't forget to change your RADIUS rules if you moved your WiFi APs into the 192.168.3.0/24 subnet. You'll also need to edit /etc/raddb/clients.conf
I used a new table here called "raw". This table is more primitive than the filter table. It cannot have FORWARD rules or INPUT rules. Therefore you will still need a FORWARD rule in your filter table to block bogons originating from your LAN.
The only kind of rules we may use here are PREROUTING and OUTPUT. The OUTPUT rules will only filter traffic originating from our router's local processes, such as if we ran the ping command to a bogon range on the router's command prompt.
Traffic passes over the raw table, before connecting marking as indicated by this packet flow map: Netfilter packet flow graph this means we don't have to strip the mark off the bogon range in the mangle table anymore.
######################################################################### # Advanced routing rule set # Uses 192.168.1.0 via ISP # 192.168.2.0 via VPN # 192.168.3.0 via LAN # # Packets to/from 192.168.1.0/24 are marked with 0x1 and routed to ISP # Packets to/from 192.168.2.0/24 are marked with 0x2 and routed to VPN # Packets to/from 192.168.3.0/24 are routed to LAN and not forwarded onto # the internet # ######################################################################### # # Raw Table # This table is the place where we drop all illegal packets from networks that # do not exist # *raw :PREROUTING ACCEPT [0:0] :OUTPUT ACCEPT [0:0] # Create a log drop chain :LOG_DROP_BOGON - [0:0] # Create an output chain :OUT_PPP0 - [0:0] :OUT_TUN0 - [0:0] # Allows traffic from VPN tunnel -A PREROUTING -s 172.16.32.0/20 -i tun0 -j ACCEPT # Allows traffic to VPN tunnel -A PREROUTING -d 172.16.32.0/20 -j ACCEPT # Block specified bogons coming in from ISP and VPN # (unlikely to happen as they filter them on their router) -A PREROUTING -i ppp0 -m set --match-set bogon-bn-nonagg src -j LOG_DROP_BOGON -A PREROUTING -i tun0 -m set --match-set bogon-bn-nonagg src -j LOG_DROP_BOGON # Allows my excepted ranges. -A PREROUTING -m set --match-set allowed-nets-ipv4 src,src -j ACCEPT # Pass output interface to corresponding chain -A OUTPUT -o ppp0 -j OUT_PPP0 -A OUTPUT -o tun0 -j OUT_TUN0 # Log drop chain -A LOG_DROP_BOGON -j LOG --log-prefix "Dropped Bogon (ipv4) : " --log-level 6 -A LOG_DROP_BOGON -j DROP # Block packets originating from the router destined to bogon ranges -A OUT_PPP0 -m set --match-set bogon-bn-nonagg dst -j LOG_DROP_BOGON # Blocks packets originating from the router destined to bogon ranges -A OUT_TUN0 -d 172.16.32.0/20 -j ACCEPT -A OUT_TUN0 -m set --match-set bogon-bn-nonagg dst -j LOG_DROP_BOGON COMMIT # # NAT Table # This is where translation of packets happens as well as "forwarding" of ports # to specific hosts. # *nat :PREROUTING ACCEPT [0:0] :INPUT ACCEPT [0:0] :OUTPUT ACCEPT [0:0] :POSTROUTING ACCEPT [0:0] # Port forwarding for Bittorrent -A PREROUTING -i tun0 -p tcp -m tcp --dport 6881:6889 -j DNAT --to-destination 192.168.2.20 -A PREROUTING -i tun0 -p udp -m udp --dport 6881:6889 -j DNAT --to-destination 192.168.2.20 # Allows routing to our modem subnet so we can access the web interface -A POSTROUTING -s 192.168.1.0/24 -d 192.168.0.1/32 -o eth1 -p tcp -m tcp --dport 80 -j MASQUERADE -A POSTROUTING -s 192.168.2.0/24 -d 192.168.0.1/32 -o eth1 -p tcp -m tcp --dport 80 -j MASQUERADE # Allows hosts of the network to use the VPN tunnel -A POSTROUTING -o tun0 -j MASQUERADE # Allows hosts of the network to use the PPP tunnel -A POSTROUTING -o ppp0 -j MASQUERADE COMMIT # # Filter Table # This is where we decide to ACCEPT, DROP or REJECT packets # *filter :INPUT DROP [0:0] :FORWARD DROP [0:0] :OUTPUT ACCEPT [0:0] # Create rule chain per input interface for forwarding packets :FWD_ETH0 - [0:0] :FWD_ETH1 - [0:0] :FWD_PPP0 - [0:0] :FWD_TUN0 - [0:0] # Create rule chain per input interface for input packets (for host itself) :IN_ETH0 - [0:0] :IN_ETH1 - [0:0] :IN_PPP0 - [0:0] :IN_TUN0 - [0:0] # Create a drop chain :LOG_DROP - [0:0] # Create a log drop chain :LOG_DROP_BOGON - [0:0] # Create a reject chain :LOG_REJECT_LANONLY - [0:0] # Create an output chain :OUT_PPP0 - [0:0] :OUT_TUN0 - [0:0] # Pass input packet to corresponding rule chain -A INPUT -i lo -j ACCEPT -A INPUT -i eth0 -j IN_ETH0 -A INPUT -i eth1 -j IN_ETH1 -A INPUT -i ppp0 -j IN_PPP0 -A INPUT -i tun0 -j IN_TUN0 # Track forwarded packets -A FORWARD -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT # Pass forwarded packet to corresponding rule chain -A FORWARD -i eth0 -j FWD_ETH0 -A FORWARD -i eth1 -j FWD_ETH1 -A FORWARD -i ppp0 -j FWD_PPP0 -A FORWARD -i tun0 -j FWD_TUN0 # Pass output interface to corresponding chain -A OUTPUT -o ppp0 -j OUT_PPP0 -A OUTPUT -o tun0 -j OUT_TUN0 # Forward traffic to Modem -A FWD_ETH0 -d 192.168.0.1/32 -j ACCEPT # Allow routing to remote address on VPN -A FWD_ETH0 -s 192.168.1.0/24 -d 172.16.32.1/32 -o tun0 -j ACCEPT -A FWD_ETH0 -s 192.168.2.0/24 -d 172.16.32.1/32 -o tun0 -j ACCEPT # Allow forwarding from LAN hosts to LAN ONLY subnet -A FWD_ETH0 -s 192.168.1.0/24 -d 192.168.3.0/24 -j ACCEPT -A FWD_ETH0 -s 192.168.2.0/24 -d 192.168.3.0/24 -j ACCEPT # Allow LAN ONLY subnet to contact other LAN hosts -A FWD_ETH0 -s 192.168.3.0/24 -d 192.168.1.0/24 -j ACCEPT -A FWD_ETH0 -s 192.168.3.0/24 -d 192.168.2.0/24 -j ACCEPT # Refuse to forward bogons to the internet! -A FWD_ETH0 -m set --match-set bogon-bn-nonagg dst -j LOG_DROP_BOGON # Forward traffic to ISP -A FWD_ETH0 -s 192.168.1.0/24 -j ACCEPT # Forward traffic to VPN -A FWD_ETH0 -s 192.168.2.0/24 -j ACCEPT # Prevent 192.168.3.0/24 from accessing internet -A FWD_ETH0 -s 192.168.3.0/24 -j LOG_REJECT_LANONLY # Allow excepted server to be FORWARD to ppp0 #-A FWD_ETH0 -s 192.168.2.0/24 -d <IP_OF_EXCEPTED_SERVER>/32 -o ppp0 -j ACCEPT # Forward SSH packets from network to modem -A FWD_ETH1 -s 192.168.0.1/32 -d 192.168.1.0/24 -p tcp -m tcp --sport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A FWD_ETH1 -s 192.168.0.1/32 -d 192.168.2.0/24 -p tcp -m tcp --sport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Forward HTTP packets from network to mode -A FWD_ETH1 -s 192.168.0.1/32 -d 192.168.1.0/24 -p tcp -m tcp --sport 80 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A FWD_ETH1 -s 192.168.0.1/32 -d 192.168.2.0/24 -p tcp -m tcp --sport 80 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Forward Bittorrent Port to workstation -A FWD_TUN0 -d 192.168.2.20/32 -p tcp -m tcp --dport 6881:6889 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A FWD_TUN0 -d 192.168.2.20/32 -p udp -m udp --dport 6881:6889 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # SSH to Router -A IN_ETH0 -s 192.168.1.0/24 -p tcp -m tcp --dport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A IN_ETH0 -s 192.168.2.0/24 -p tcp -m tcp --dport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # DNS to Router -A IN_ETH0 -s 192.168.1.0/24 -p udp -m udp --dport 53 -m conntrack --ctstate NEW -j ACCEPT -A IN_ETH0 -s 192.168.2.0/24 -p udp -m udp --dport 53 -m conntrack --ctstate NEW -j ACCEPT # FreeRadius Client (eg a UniFi AP) -A IN_ETH0 -s 192.168.3.10/32 -p tcp -m tcp --dport 1812 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A IN_ETH0 -s 192.168.3.10/32 -p udp -m udp --dport 1812 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Ubiquiti UAP Device Discovery Broadcast -A IN_ETH0 -s 192.168.3.10/32 -p udp -m udp --dport 10001 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # NTP to Router -A IN_ETH0 -s 192.168.1.0/24 -p udp -m udp --dport 123 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A IN_ETH0 -s 192.168.2.0/24 -p udp -m udp --dport 123 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A IN_ETH0 -s 192.168.3.0/24 -p udp -m udp --dport 123 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Accept traffic to router on both subnets -A IN_ETH0 -s 192.168.1.0/24 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT -A IN_ETH0 -s 192.168.2.0/24 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Allow excepted server to be INPUT to eth0 from LAN #-A IN_ETH0 -s 192.168.2.0/24 -d <IP_OF_EXCEPTED_SERVER>/32 -o ppp0 -j ACCEPT # SSH To Modem from Router -A IN_ETH1 -s 192.168.0.1/32 -d 192.168.0.0/30 -p tcp -m tcp --sport 22 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # HTTP To Modem from Router -A IN_ETH1 -s 192.168.0.1/32 -d 192.168.0.0/30 -p tcp -m tcp --sport 80 -m conntrack --ctstate NEW,ESTABLISHED -j ACCEPT # Accept incoming tracked PPP0 connection -A IN_PPP0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT # Log dropped packets coming in on PPP0 -A IN_PPP0 -j LOG --log-prefix "DROP:INPUT (ipv4) " --log-level 6 -A IN_PPP0 -j LOG_DROP # Accept incoming tracked TUN0 connection -A IN_TUN0 -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT # Log dropped packets coming in on TUN0 -A IN_TUN0 -j LOG --log-prefix "DROP:INPUT (ipv4) " --log-level 6 -A IN_TUN0 -j LOG_DROP # Log dropped bogons that never got forwarded -A LOG_DROP_BOGON -j LOG --log-prefix "Dropped Bogon forward (ipv4) " --log-level 6 -A LOG_DROP_BOGON -j DROP # Log rejected packets -A LOG_REJECT_LANONLY -j LOG --log-prefix "Rejected packet from LAN only range : " --log-level 6 -A LOG_REJECT_LANONLY -j REJECT --reject-with icmp-port-unreachable COMMIT # # Mangle Table # This is the place where our markings happen, whether they be 0x1 or 0x2 # *mangle # Set default policies for table :PREROUTING ACCEPT [0:0] :INPUT ACCEPT [0:0] :FORWARD ACCEPT [0:0] :OUTPUT ACCEPT [0:0] :POSTROUTING ACCEPT [0:0] # Restore CONNMARK to the MARK (If one doesn't exist then no mark is set) -A PREROUTING -j CONNMARK --restore-mark --nfmask 0xffffffff --ctmask 0xffffffff # If packet MARK is 2, then it means there is already a connection mark and the # original packet came in on VPN -A PREROUTING -s 192.168.2.0/24 -m mark --mark 0x2 -j ACCEPT # Check exception (this is a server which when accessed on a 192.168.2.0/24 address will go out the ISP table) are 0x1 #-A PREROUTING -s 192.168.2.0/24 -d <IP_OF_EXCEPTED_SERVER>/32 -m mark --mark 0x1 -j ACCEPT # Mark packets coming from 192.168.2.0/24 are 0x2 -A PREROUTING -s 192.168.2.0/24 -j MARK --set-xmark 0x2/0xffffffff # If packet MARK is 1, then it means there is already a connection mark and the # original packet came in on ISP -A PREROUTING -s 192.168.1.0/24 -m mark --mark 0x1 -j ACCEPT # Mark packets 192.168.1.0/24 are 0x1 -A PREROUTING -s 192.168.1.0/24 -j MARK --set-xmark 0x1/0xffffffff # Mark exception (this is a server which when accessed on a 192.168.2.0/24 address will go out the ISP table) as 0x1 #-A PREROUTING -s 192.168.2.0/24 -d <IP_OF_EXCEPTED_SERVER>/32 -j MARK --set-xmark 0x1/0xffffff # Strip mark if packet is destined for modem -A PREROUTING -d 192.168.0.1/32 -j MARK --set-xmark 0x0/0xffffffff # Save MARK to CONNMARK (remember iproute can't see CONNMARKs) -A PREROUTING -j CONNMARK --save-mark --nfmask 0xffffffff --ctmask 0xffffffff COMMIT
Other Tips
Diagnosing firewall problems
netcat, netcat6
Netcat can be useful for testing if a port is open or closed or filtered.
apk add netcat-openbsd
After installing netcat, we can use it like this:
Say we wanted to test for IPv6, UDP, Port 547 we would do this on the router:
nc -6 -u -l 547
and then this on the client to connect to it:
nc -u -v -6 2001:0db8:1234:0001::1 547
tcpdump
tcpdump can also be useful for dumping the contents of packets coming in on an interface:
apk add tcpdump
Then we can run it. This example captures all DNS traffic originating from 192.168.2.20.
tcpdump -i eth0 udp and src 192.168.2.20 and port 53
You can write the file out with the -w option, and view it in Wireshark locally on your computer. You can increase the verbosity with the -v option. Using -vv will be even more verbose. -vvv will show even more.
lbu cache
Configure lbu cache so that you don't need to download packages when you restart your router eg Local APK cache
This is particularly important as some of the images do not contain ppp-pppoe. This might mean you're unable to get an internet connection to download the other packages on boot.
lbu encryption /etc/lbu/lbu.conf
In /etc/lbu/lbu.conf you might want to enable encryption to protect your VPN keys.
# what cipher to use with -e option DEFAULT_CIPHER=aes-256-cbc # Uncomment the row below to encrypt config by default ENCRYPTION=$DEFAULT_CIPHER # Uncomment below to avoid <media> option to 'lbu commit' # Can also be set to 'floppy' LBU_MEDIA=mmcblk0p1 # Set the LBU_BACKUPDIR variable in case you prefer to save the apkovls # in a normal directory instead of mounting an external medium. # LBU_BACKUPDIR=/root/config-backups # Uncomment below to let lbu make up to 3 backups # BACKUP_LIMIT=3
Remember to set a root password, by default Alpine Linux's root account is passwordless.
passwd root
Backup apkprov
It's a good idea to back up your apk provision file. You can pull it from your router to your local workstation with:
scp -r root@192.168.2.1:/media/mmcblk0p1/<YOUR HOST NAME>.apkovl.tar.gz.aes-256-cbc ./
And decrypt it with:
openssl enc -d -aes-256-cbc -in <YOUR HOST NAME>.apkovl.tar.gz.aes-256-cbc -out <YOUR HOST NAME>.apkovl.tar.gz
It can be encrypted with:
openssl aes-256-cbc -salt -in <YOUR HOST NAME>.apkovl.tar.gz -out <YOUR HOST NAME>.apkovl.tar.gz.aes-256-cbc
Harden SSH
Generate a SSH key
ssh-keygen -t rsa -b 4096
You will want to put the contents of id_rsa.pub in /etc/ssh/authorized_keys
You can put multiple public keys on multiple lines if more than one person has access to the router.
/etc/ssh/sshd_config
A couple of good options to set in here can be:
ListenAddress 192.168.1.1 ListenAddress 192.168.2.1
While this isn't usually a good idea, a router doesn't need more than one user.
PermitRootLogin yes
The most important options:
RSAAuthentication yes PubkeyAuthentication yes AuthorizedKeysFile /etc/ssh/authorized_keys PasswordAuthentication no PermitEmptyPasswords no AllowTcpForwarding no X11Forwarding no
/etc/conf.d/sshd
You will want to add
rc_need="net"
This instructs OpenRC to make sure the network is up before starting SSH.
Finally add sshd to the default run level
rc-update add sshd default
Additionally you may want to look at Secure Secure Shell and tighten OpenSSH's cryptography options.